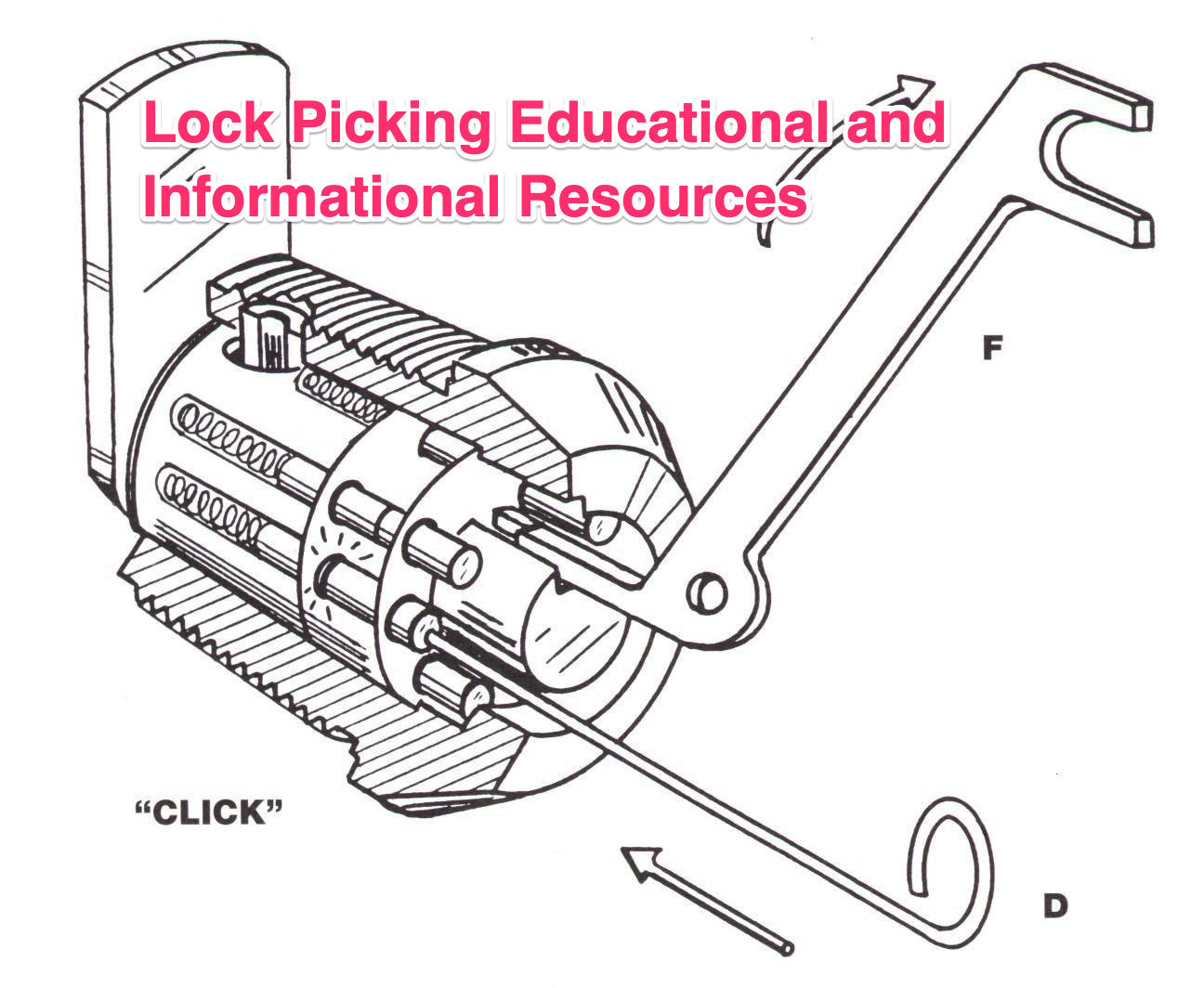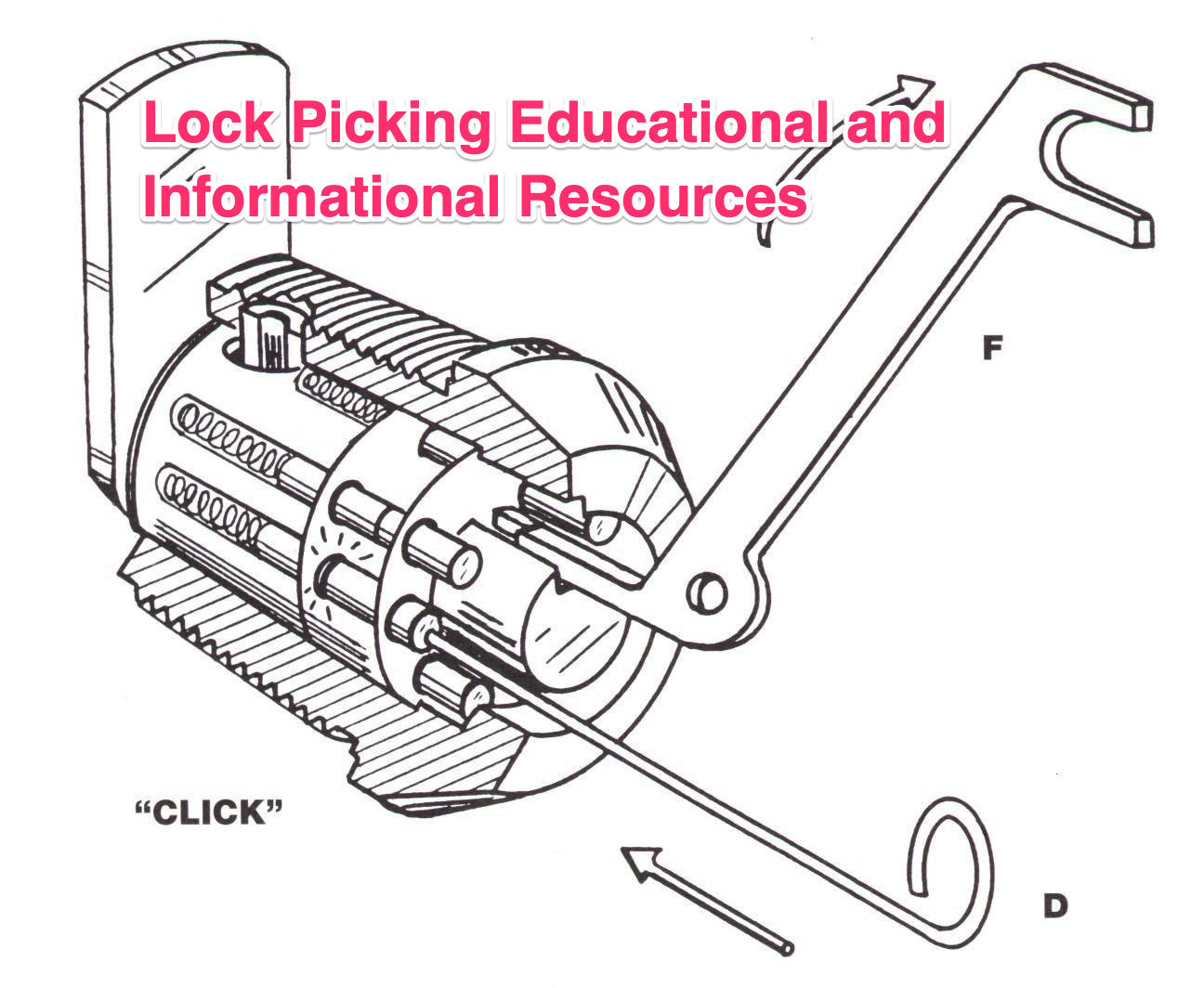
All lock picking content is for educational and informational use only.
Underwriters Laboratories defines the different types of locks for which the specification applies.
Product: This refers to any type of lock or component defined within the standard:
Door Lock: This is a rim or mortise-type locking assembly that is used on doors to deter unauthorized opening by one or more of the following means:
∑ Jimmying the door;
∑ Picking;
∑ Impressioning techniques;
∑ Driving the locking cylinder or assembly;
∑ Sawing or drilling the lock bolt;
∑ Pulling the lock cylinder;
∑ Other methods that involve the use of small hand-tools.
Locking Cylinder: A key-cylinder that is used within door locks, alarm control switches, alarm shunt switches, utility locks, and similar devices to resist unauthorized opening by one or more of the following techniques:
∑ Picking;
∑ Impressioning techniques;
∑ Forcing methods;
∑ Pulling;
∑ Drilling the cylinder.
Security Container Key Lock: This is a lock that is designed for use on key-locked safes, collection safes, and similar security containers to resist methods of entry that include:
∑ Picking;
∑ Impressioning;
∑ Drilling;
∑ Pulling;
∑ Punching;
∑ Forcing methods.
General Construction and Operating Requirements
UL specifies a number of requirements that relate to the construction and operation of any lock that is certified under this standard. These include:
∑ The product shall be constructed so that it may be readily and conveniently operated when the proper key or keys are used;
∑ The lock must be practicable for installation by a trained locksmith, and able to be installed in a position or location that does not degrade its burglary-resistant qualities;
∑ Parts must maintain a high degree of tolerance and uniformity. This is especially important with regard to bittings.
Locks tested under UL 437 must be constructed of brass, bronze, stainless steel, or equivalent corrosion-resistant material, or shall have a protective finish that meets salt spray tests.
There are a number of common standards relating to locks and security containers, including requirements relating to nonmetallic parts, corrosion protection, and salt spray. These are described in UL 768.
Specific Requirements for Locks
Differs
Door locks and cylinders must be capable of at least 1000 key changes. Security containers must achieve significantly higher security levels, providing at least 1,000,000 differs for any design. Two-key locks require a minimum of 64 guard key changes, and at least 15,000 customer key changes for any design.
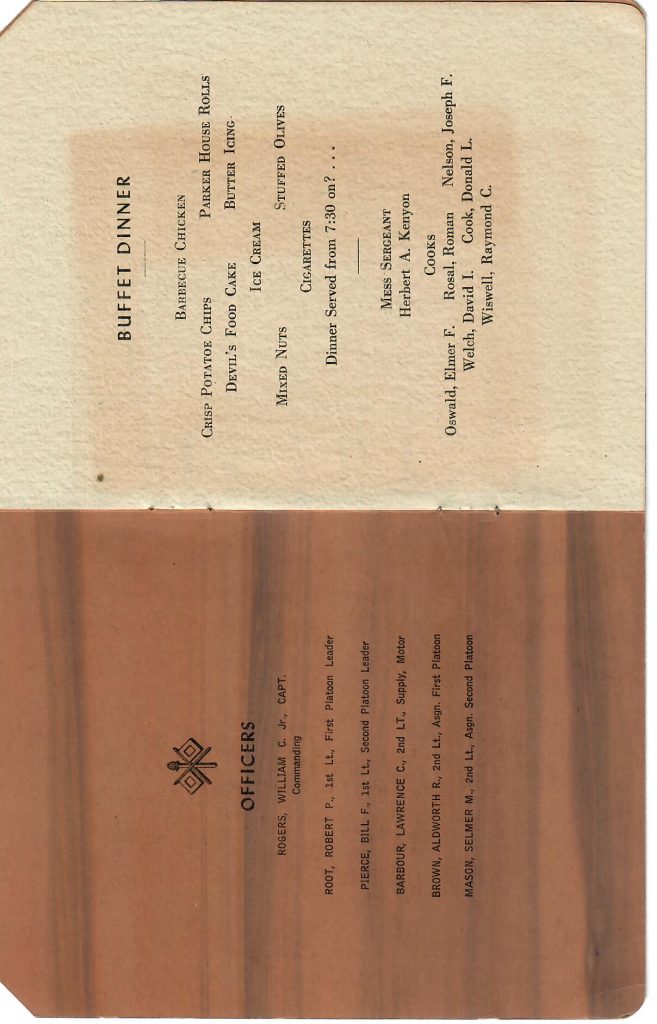
Security Container Key-Locks
Specific requirements for locks that are utilized on security containers include:
∑ Key shall be field changeable;
∑ The bolt lever must fit snugly on its post and shall be secured tightly;
∑ The fence face shall be perpendicular to the plane of the tumblers;
∑ The wheels, tumblers, levers, or pins shall run true, and be at right angles to their mounting post;
∑ Within a combination-lock, the clearance between the fence face and the tumbler wheels shall not be less than .025î (0.64 mm) when the bolt lever is raised by means of a driver cam, and not less than .015î (0.38 mm) when the bolt lever is raised by means other than a driver cam;
∑ Mechanical means must be provided that immobilizes the bolt if the lock is punched or pulled;
∑ The tolerance between plug and shell in a pin tumbler lock must be less than one cut depth.
Endurance Test
The lock shall function as intended during 10,000 complete cycles of operation at a rate not exceeding 50 cycles per minute;
A lock having a changeable core or field-changeable key design shall operate as intended after each of 50 changes of the core or key.
Attack Resistance Tests
Attack resistance tests encompass setup requirements, use of specified tools, timing, and entry methods.
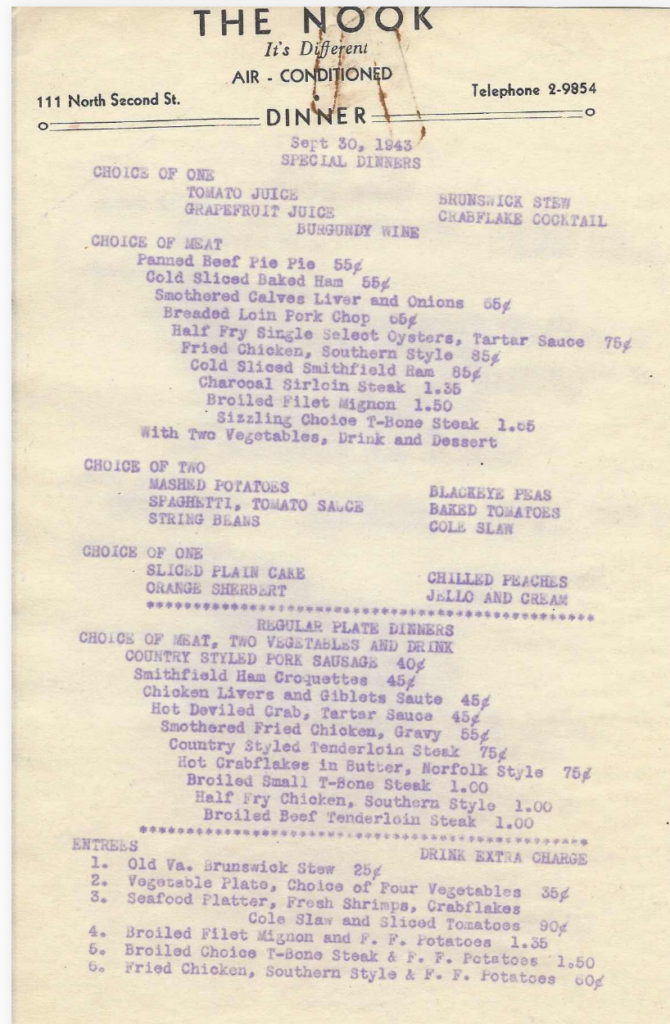
Test Requirements
A number of tests have been defined to ascertain the attack resistance of a lock. UL 437 requires that a device cannot be opened or compromised as a result of the application or use of tools and techniques set forth in the standard, and summarized here.
Specific protocols have been devised with respect to mounting of samples to be tested. Door locks must be installed in accordance with the lock manufacturer’s instructions, in a 1-1/2î (38.1 mm) solid hardwood door of average size. The door is mounted in a 1-1/4î (38.1 mm) thick wood frame and reinforced as if actually installed. Door locks that are designed specifically for a certain door construction are to be tested in that mode.
The following test requirements apply for attack ratings:
∑ The tools used for these tests include any common hand tools, hand or portable electric tools, drills, saw blades, puller mechanisms, and picking tools. For door locks only, pry bars up to three feet (.9 meter) long are also to be employed;
∑ Tools that are used on two-key locks must not include saws, puller mechanisms, or portable electric drills;
∑ Common hand tools are defined as chisels, screwdrivers no more than 15î (380 mm) long, hammers having three-pound (1.36 kg) head weight, jaw-gripping wrenches, and pliers;
∑ Puller devices are to be either a slam-hammer mechanism, having a maximum head weight of three pounds (1.36 kg), or a screw type;
∑ Picking tools are common or standard patterns, as well as those designed for use on a particular make or design of cylinder;
∑ Portable electric tools are identified as high-speed handheld drills that meet the following criteria:
∑ Operate at a maximum of 1900 RPM;
∑ Maximum ºî (6.4 mm) chuck size;
∑ Use high-speed drill bits;
∑ Utilize electrically operated vibrating needles.
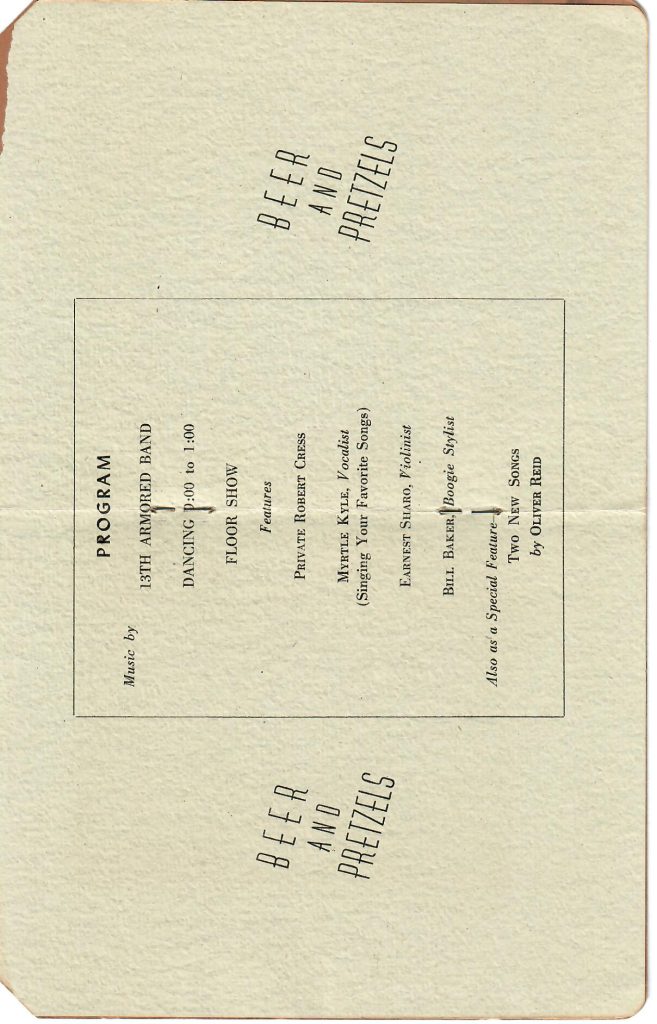
Test Time for Attack Resistance
Net times in minutes are specified for each type of test, and the lock upon which the procedure is to be performed. The sequence is not relevant, nor the number of methods to be applied. Samples may be tested for several techniques, or a new specimen may be utilized for each procedure. Below are the results in time it takes to work to break a lock.
| Test | Door Locks/Cylinders | Security Container Key Locks | Two-Key Locks |
| Picking | 10 | 30 | 45 |
| Impressioning | 10 | 30 | 45 |
| Forcing | 5 | 30 | 5 |
| Drilling | 5 | 30 | NA |
| Sawing | 5 | 30 | NA |
| Prying | 5 | 30 | NA |
| Pulling | 5 | 30 | NA |
| Driving | 5 | 30 | NA |
Test Methods
There are eight methods of forced and direct entry that are defined within the Standard: picking, impressioning, forcing, drilling, sawing, prying, pulling, and driving. These have been previously described in Chapters 29-32.
Picking
Picking tools are employed in an attempt to align the active components, including tumblers, levers, wheels, or pins, in order to open the lock.
Impressioning
Methods of impressioning, as defined in Chapter 31, are employed in an attempt to produce working keys.
Forcing
Rotary forces are applied with the test tools in three critical areas, in an attempt to open the target lock:
∑ In the key slot;
∑ On the exposed part of the cylinder;
∑ On the exposed portions of the lock assembly.
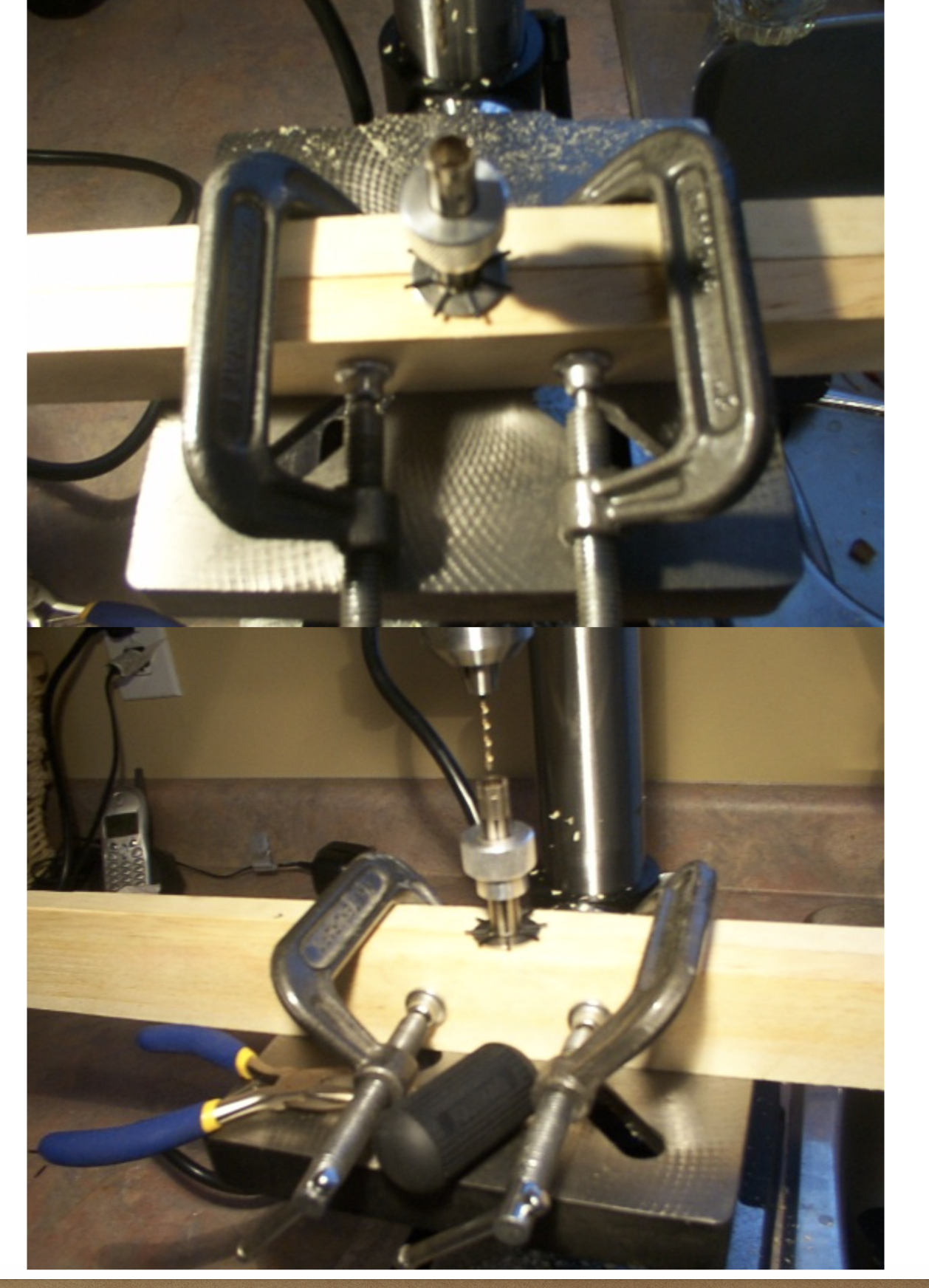
Drilling
Drilling requires that a drill and one or more bits are utilized to attack the plug, exposed lock body, and other parts in an attempt to compromise critical components to effect an opening.
Sawing
A saw is employed in an effort to cut, compromise, remove, and open critical components, including the plug, body of the cylinder, and lock bolt.
Prying
Tools are utilized in an attempt to pry the bolt out of engagement with the strike opening within a door lock assembly.
Pulling
Techniques of pulling are directed at critical locking components including the plug, body, bolt, or other areas in order to compromise and open the device.
Driving
Driving is the opposite of pulling. Tools are utilized in an attempt to drive or force the plug, body of the lock, lock bolt, or other part to allow bypass of the mechanism.