Computer Science Lesson Plans
As part of providing lesson plans for teachers. Students may also wish to work with Arduinos. Most of the lessons outlined require the use of the computer. There are some lessons, though, that are offline only.
Computer Science Lesson Plans: The Internet
| Lesson 1: The Internet is for Everyone Primary Source Reading Assignment: The Internet is for Everyone |
Lesson 2: The Need for Addressing | Lesson 3:Invent an Addressing Protocol | Lesson 4: Routers and Redundancy |
| Lesson 5: Packets and Making a Reliable Internet Peter the Packet Game |
Lesson 6: Algorithms Detour – Minimum Spanning Tree | Lesson 7: Algorithms Detour – Shortest Path
Intro to the Shortest Path Problem Intro Dijkstras Shortest Path Algorithm Dijkstras Shortest Path Algorithm A Dijkstras Shortest Path Algorithm B Dijkstras Shortest Path Algorithm C Dijkstras Shortest Path Algorithm D Dijkstras Shortest Path Algorithm E Dijkstras Shortest Path Algorithm F |
Lesson 8: How Routers Learn |
| Lesson 9: The Need for DNS | Lesson 10: DNS in the Real World | Lesson 11: HTTP and Abstraction on the Internet
-Homework: Blown to Bits Questions |
Lesson 12: Global Impacts of the Internet
Rubric for Global Impact of the Internet Project Resource Topic List for Global Impact of the Internet Project Writing Directions Worksheet for Global Impacts of the Internet Project |
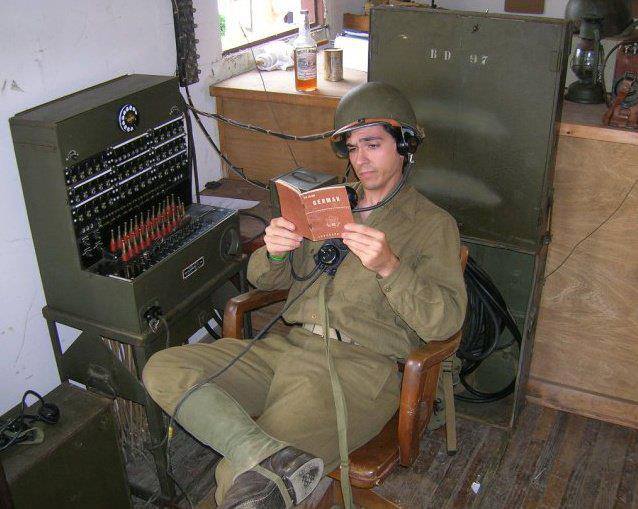
| Lesson 13: The Need for Encryption –Encryption Questions: Complete first two pages only –Blown to Bits Reading Encryption–12-2 Caesar Cipher Assignment |
Lesson 14: Cracking the Code: | Lesson 15: Keys and Passwords | Lesson 16: Hard Problems – The Traveling Salesperson Problem |
| Lesson 17: One Way Functions – The WiFi Hotspot Problem | Lesson 18: Asymmetric Keys – Cups and Beans
Homework: |
Lesson 19: Public Key Cryptography | Lesson 20: Practice performance task – Security and Hacking in the Real World |
Computer Science Lesson Plans: Digital Information Unit
| Lesson 1: Personal Innovations | Lesson 2:Sending Simple Binary Messages | Lesson 3: Sending Complex Binary Messages | Lesson 4:
Sending Binary Messages with the Internet Simulator Homework |
Lesson 5: Sending Bits in the Real World | Lesson 6: Number Systems |
| Lesson 7: Binary Numbers |
Lesson 8: Sending Numbers |
Lesson 9: Encoding Numbers in Real WorldResearch Activity |
Lesson 10: Encoding and Sending Text | Lesson 11: Sending Formatted Text
Blown to Bits: Chapter 3_pg_73-80-What You See Is Not What the Computers Knows Blown to Bits 10 Questions on Chapter 3 Reading (Google Doc) |
Lesson 12: Bytes and File Sizes |
| Lesson 13: Text Compression | Lesson 14: Encoding Black and White Images | Lesson 15: Encoding Color ImagesBlown to Bits Reading: Hiding Information in Images (pdf)Blown to Bits Questions: Hiding Information in Images(Google Doc) |
Second Quarter Project: | Lesson 16: Lossy Compression and File Formats | Lesson 17: Encode a Complex Thing |